2011-06-01
Abstract
A new method of targeted attack has recently been discovered in which the auto preview feature of Google Images is utilized to lure the user into downloading and purchasing fake AV applications. Robert X Wang has the details.
Copyright © 2011 Virus Bulletin
Fake AV is a term used to describe threats which masquerade as real security products, fooling victims into believing that they have discovered infections on their machines. The ‘products’ then insist on payment for an activation/registration code in order to clean the supposed threats from the system.
As with many other threats, social engineering techniques are often used to spread fake AV. The malicious file may have a tempting name and arrive as an email attachment, a download link, or a shared folder. However, such methods require a considerable amount of user interaction – if the user doesn’t download and execute the file, the fake AV will not be able to fool the user into believing their system is infected and subsequently generate revenue for the attacker.
A new method of targeted attack has recently been discovered in which the auto preview feature of Google Images is utilized to lure the user into downloading and purchasing the fake AV application. This method has proved to be very effective.
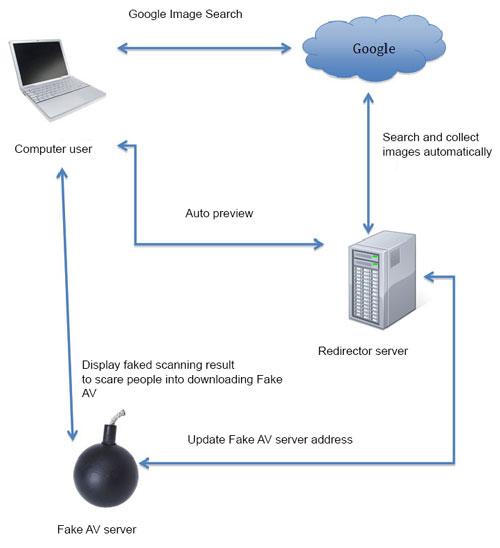
After the user has entered a keyword and clicked the ‘search’ button in Google Images, the search engine displays all the relevant images it has found. When the user clicks on an image, Google both displays the original image and previews the web page on which the image is hosted.
When an image from a malformed URL (redirector) is clicked, the redirector will examine some of the following parameters and then decide what to do next:
The referer URL in the HTTP header
The Google Image Search keyword
The User-Agent string in the HTTP header
If the referer URL is not from Google Image Search and/or the Google Image Search keyword is not detected, the redirector will display a clean web page. This tactic is used by the fake AV to prevent it from being spotted.
If the User-Agent string is not supported, the redirector will display a clean web page or else redirect to another clean page. Different types of browser will display different pages.
If all checks are passed, the redirector will send the browser to another malformed page, which lures the user into downloading the fake AV application or its downloader.
The popularity of Google Image Search makes this method extremely effective.
If any of the images shown in Figure 1 are opened, ‘hxxp://oliviercassab.com/samuri-harvest-autumn-wallpapers/’ will be loaded and previewed. If the same link is opened directly in a browser, a clean page will be displayed (Figure 2). The clean page will also be displayed if the referer URL is not from Google Images or the search keyword does not appear to be correct.
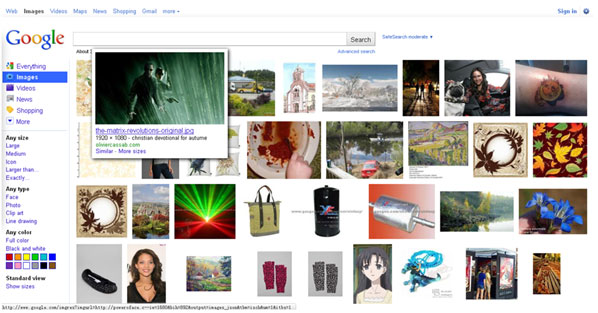
Figure 1. If any of these images are opened, hxxp://oliviercassab.com/samuri-harvest-autumn-wallpapers/ will be previewed.
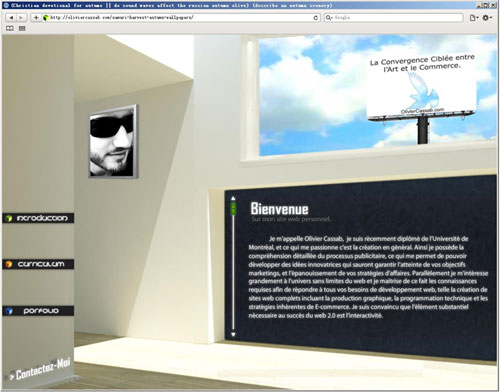
Figure 2. If the referer URL is not from Google Images or the search keyword does not appear to be correct, the redirector will display a clean page.
If the browser User-Agent string is not supported, another clean page will be displayed and the search keyword used in Google Images will be passed to the new URL (Figure 3).
Otherwise, depending on the browser User-Agent string, the user will be redirected to different sites:
All IE-based browsers and Google Chrome will be redirected to free hosting domains in the following format:
update%decimal.number%.%random.string%.%free.domain.provider%
scan%decimal.number %.%random.string%.%free.domain.provider%
For example:
scan21.goff.cz.cc
update6.ocerloh.mo.cx
All domains point to the same IP address: 212.124.119.186.
Different browsers will display different pages (see Figure 4 and Figure 5), but will lure the user into downloading a similar fake AV downloader – the file name of which is in the following format:
InstallInternetProtection_%random.3.decimal.digits%.exe
Each downloader may have a different MD5. Each comes with an encrypted download link in its appended data. The downloaded program ‘Internet Protection’ (see Figure 6 and Figure 7) then displays a series of fake alerts to lure the user into purchasing an activation code to remove the supposed threats from their machine.
Mozilla Firefox and Apple Safari are redirected to different domains with different pages and, instead of a downloader, the pages in Firefox and Safari lure the user into downloading a fake AV application (AntiSpy2011Setup.exe) directly. All domains point to the IP address 91.213.157.110. There are approximately 200 malicious domains on this IP address and the number is still increasing – the attacker registers several domains every day.
The malicious site oliviercassab.com has approximately 8,800 related images on Google Images and is far from being the only site to abuse the search service.
Another, iqsplus.com, appears to be an older version in which the redirector does not check the User-Agent string and search keyword. This uses approximately 119,000 related images on Google Images.
The owner of iqsplus.com has many other redirectors including:
beyonceknowles.eu (approx. 67,300 related images)
cinta-asia.com (approx. 33,000 related images)
zeness.com (approx. 14,600 related images)
peekspy.com (approx. 5,850 related images)
quickbuildeco.com (approx. 3,350 related images)
lynxemi.com (approx. 300 related images)